Use Cases and Deployment Scope
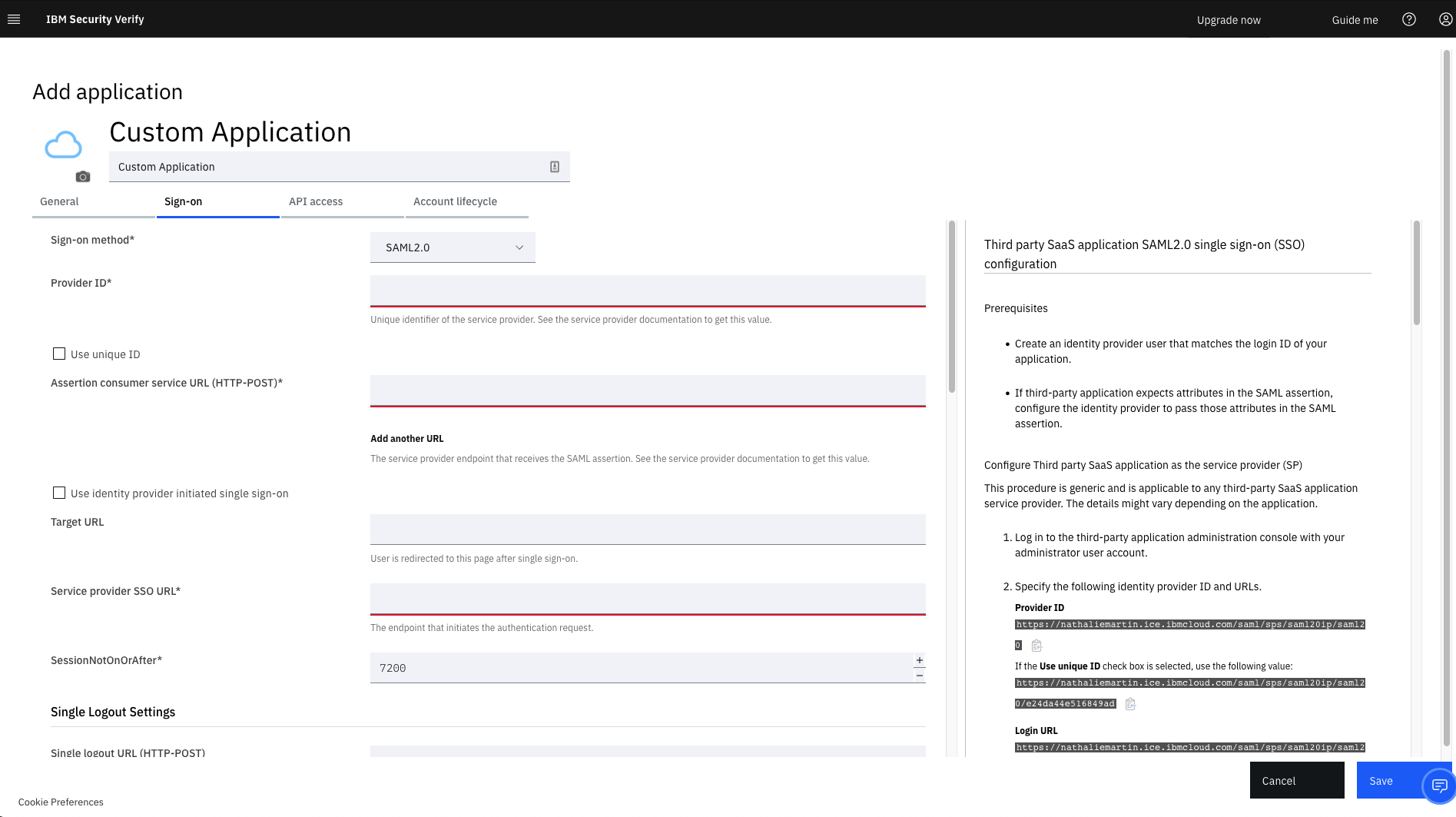
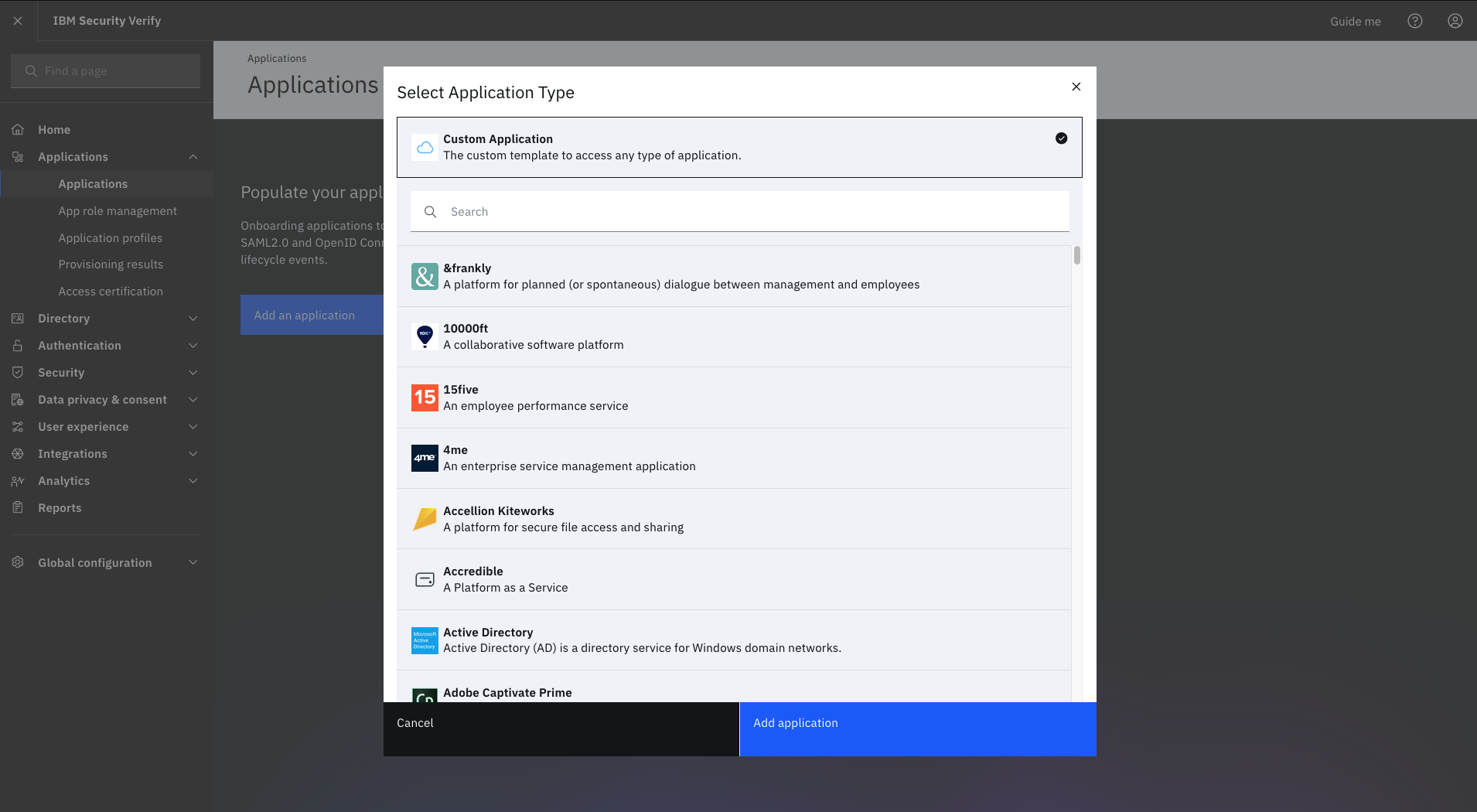
We use IBM Verify for single sign ons using multiple MFA methods like SMS, email, voice and push notifications. We like it because it helps to reduce the dependency on passwords with adaption of WebAuthn. We also use it to grant access request, approvals, onboarding and offboarding user. The ability for this platform to integrate with our legacy applications are a plus as well.
Alternatives Considered
Okta Workflows and Microsoft Entra ID
Other Software Used
Microsoft Entra ID, Okta Workflows, Auth0