Aikido Security, an indispensable tool in our security toolkit.
Use Cases and Deployment Scope
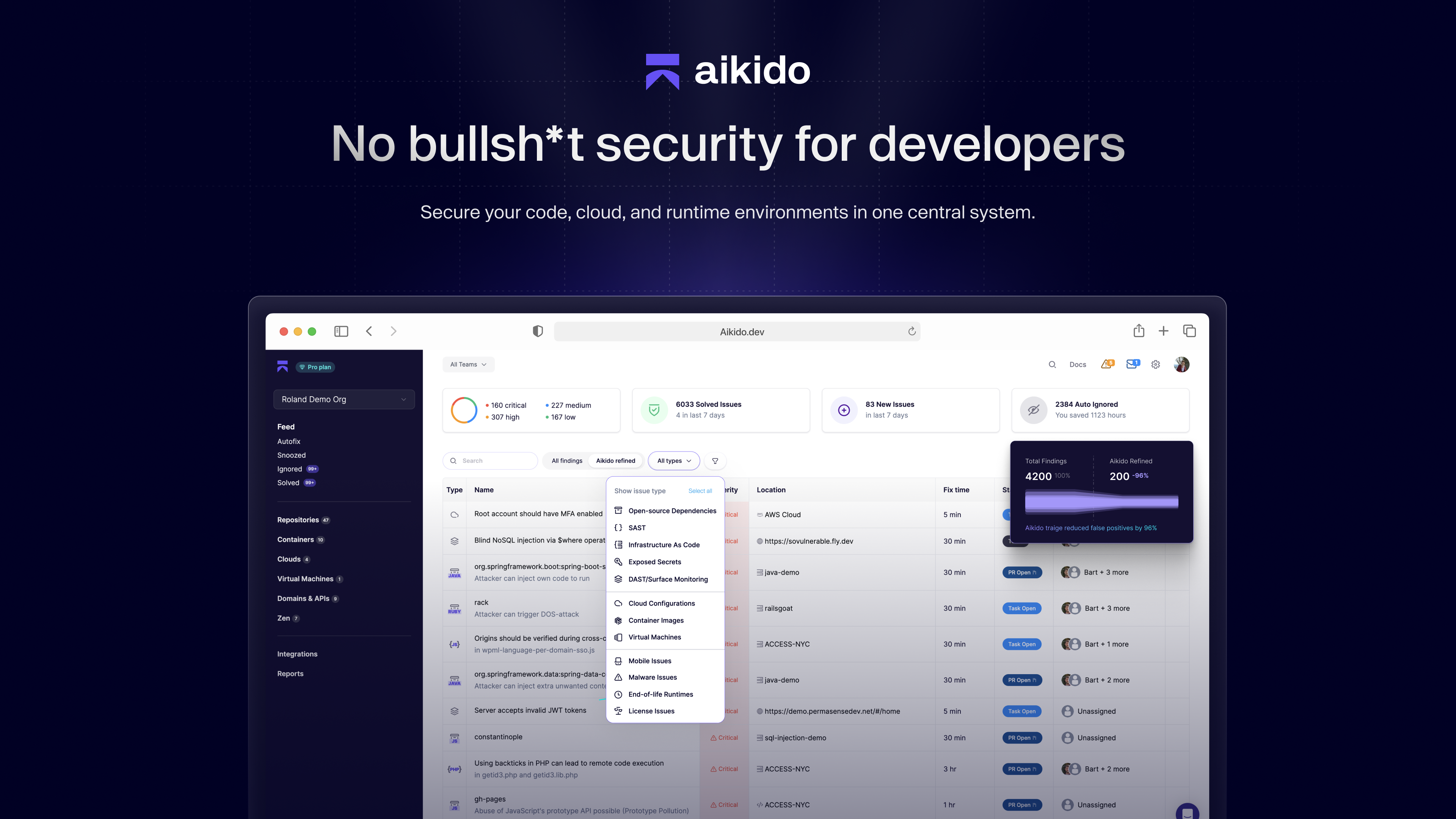
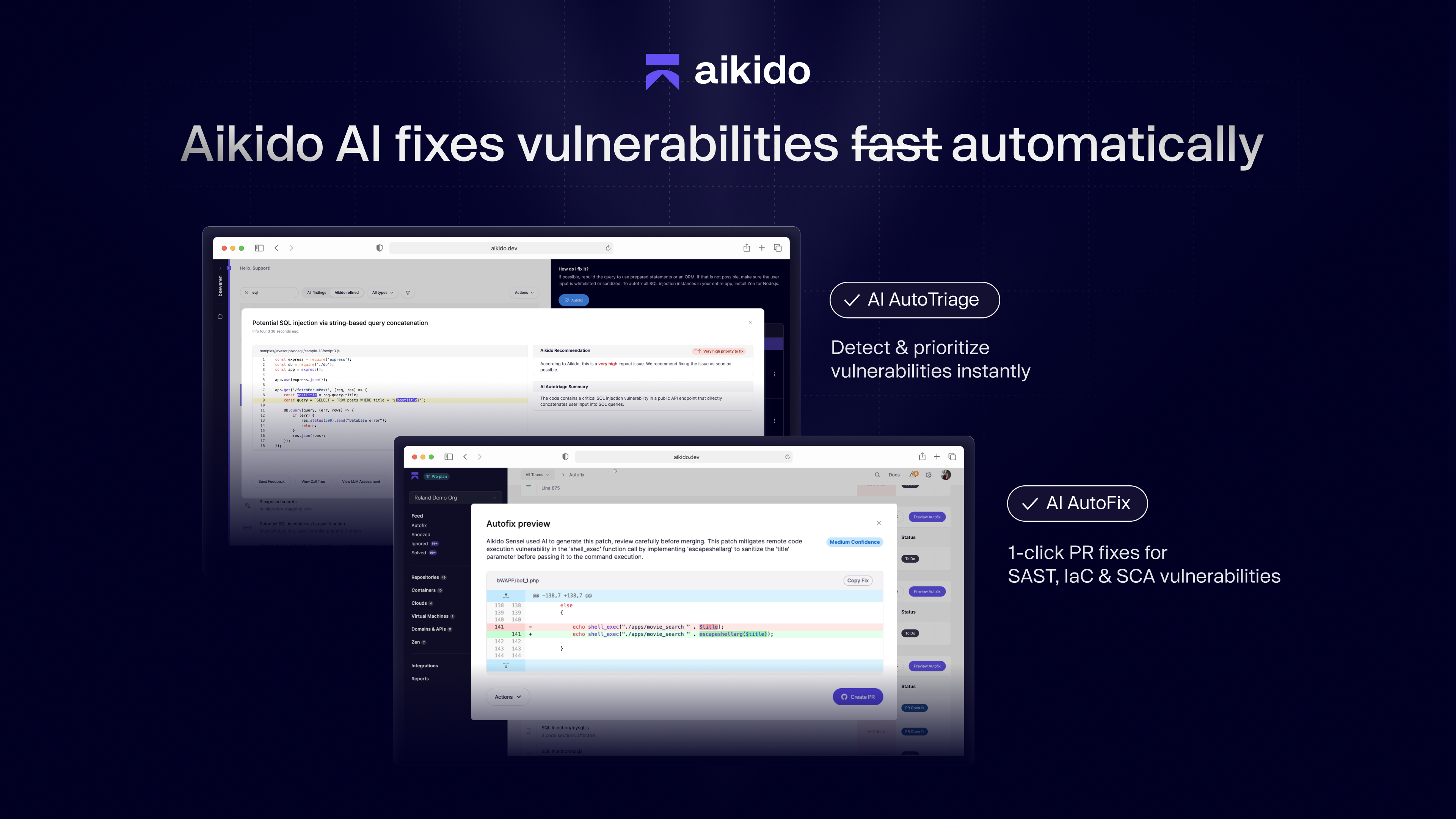
Aikido Security helps us identify and mitigate vulnerabilities before they can be exploited.
Code Security Flaws:
Aikido Security scans our codebase to detect security flaws, ensuring that potential threats are addressed early in the development cycle.
Compliance and Regulatory Requirements:
Aikido Security provides tools that help us ensure compliance.
Pros
- Engage with their customer
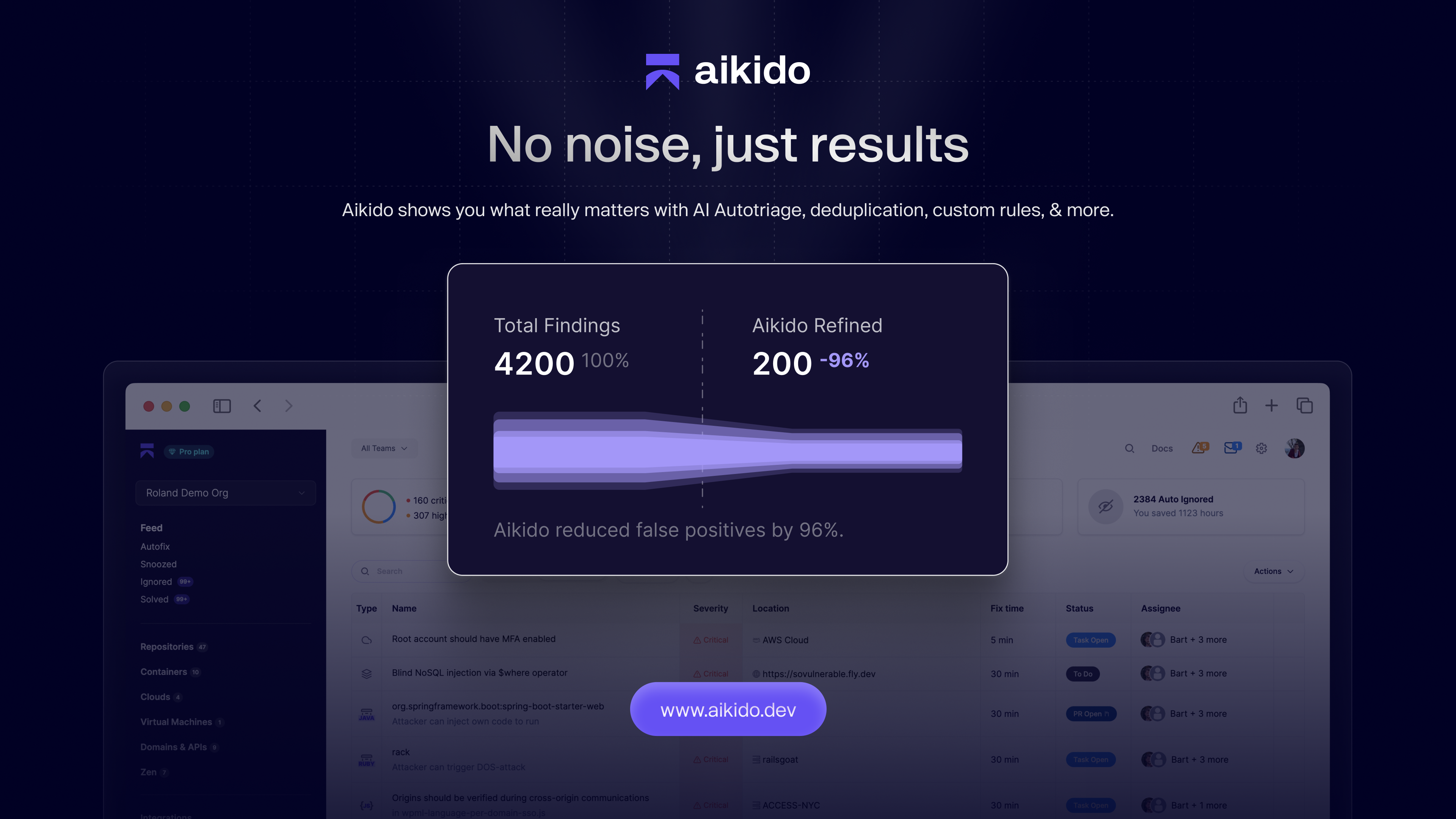
- Ease our mind, knowing that we will not be overloaded with false-positive vulnerability warnings
Cons
- It would be nice to add Aikido RMM agents to our infrastructure that report to security statusses to the Aikido cloud
Return on Investment
- By avoiding an overload of false positive vulnerability reports, we can focus on resolving the actual positives, instead of wasting time on triage